Healthcare & MedicalDevelopment Services
We provide digital solutions that solve the business needs of Healthcare startups, hospitals, and clinics.
Customers who benefit from
Our Healthcare and Medical Solutions
Hospitals/Clinics
Digital solutions for healthcare facilities
Telemedicine Providers
Virtual care and remote consultation platforms
Medical Equipment Manufacturers
Software for medical devices and equipment
Pharmaceutical Companies
Solutions for pharma and life sciences
Wellness & Fitness Companies
Digital health and wellness platforms
Healthcare Software Companies
Custom healthcare software solutions
Healthcare and
Medical Software we Develop
Organization Management Software
- •Practice and hospital management systems
- •Revenue cycle management (RCM)
- •Medical billing and claims management
- •Incident management
- •Medical inventory and asset tracking
- •Patient tracking
- •Healthcare HR and hospital staffing solutions
- •Digital workplaces for medical professionals
Care Management Software
- •EHR/EMR systems (including integration)
- •Healthcare information systems (HIS)
- •Healthcare information exchange (HIE)
- •Clinical decision support
- •Medication administration and drug prescription assistance
- •Care coordination software
- •Healthcare data analytics
Patient-Centered Software
- •Telemedicine and virtual care platforms
- •Patient engagement software
- •Patient portals (appointment scheduling, results sharing)
- •Healthcare AI chatbots
- •Chronic disease management applications
- •Remote patient monitoring systems
- •Digital therapeutics (DTx)
- •Home care software
- •Mental health apps
What we Offer
for Healthcare Institutions
Extend your web dev department
Our web development team is ready to help with your web and desktop apps, using PHP (Laravel), Python (Django), and Nuxt.
Reduce All of Your Expenses
We use AWS and best Cloud practices to launch apps and scale your projects.
Develop Native Mobile Applications
We create native iOS and Android apps with excellent user experience for your patients and staff.
Create Custom UX/UI Design
Our UX/UI Design team can help put new features into reality.
Integrate Your System with CRMs
We can help you integrate all your internal systems with the CRM systems you have.
Boost Your Product Quality
Our QA department can make sure your apps work smoothly.
Our Healthcare
Development Process
Requirement Analysis
We begin by understanding your business processes, goals, and challenges to define the scope of the Healthcare solution.
UI/UX Design
Our expert developers then design and develop a customized Healthcare project tailored to your specific requirements.
Development
Our developers build high-performance Healthcare system and solutions with a single codebase.
Testing & Quality Assurance
Rigorous testing ensures that your Healthcare solution is robust, reliable, and free from any glitches or errors.
Deployment
Our team deploy the Healthcare system seamlessly, ensuring minimal disruption to your business operations.
Training & Support
We provides comprehensive training and ongoing support to ensure a smooth transition and optimal use of the Healthcare system.
Healthcare Software Development
Technologies We Use
ERP platforms
- SAP
- Salesforce
- IFS3
- Oracle
Mobile
- Flutter
- React Native
Front-end
- Vue
- Angular
Back-end
- Net
- Java
- Python
- PHP
- Ruby
- NodeJS
- GoLand
Database
- Net
- Java
- Python
- PHP
- Ruby
- NodeJS
- GoLand
Security Standards
Products we deliver meet international security standards
Frequently Asked Questions
Common questions about healthcare software development
Case Studies
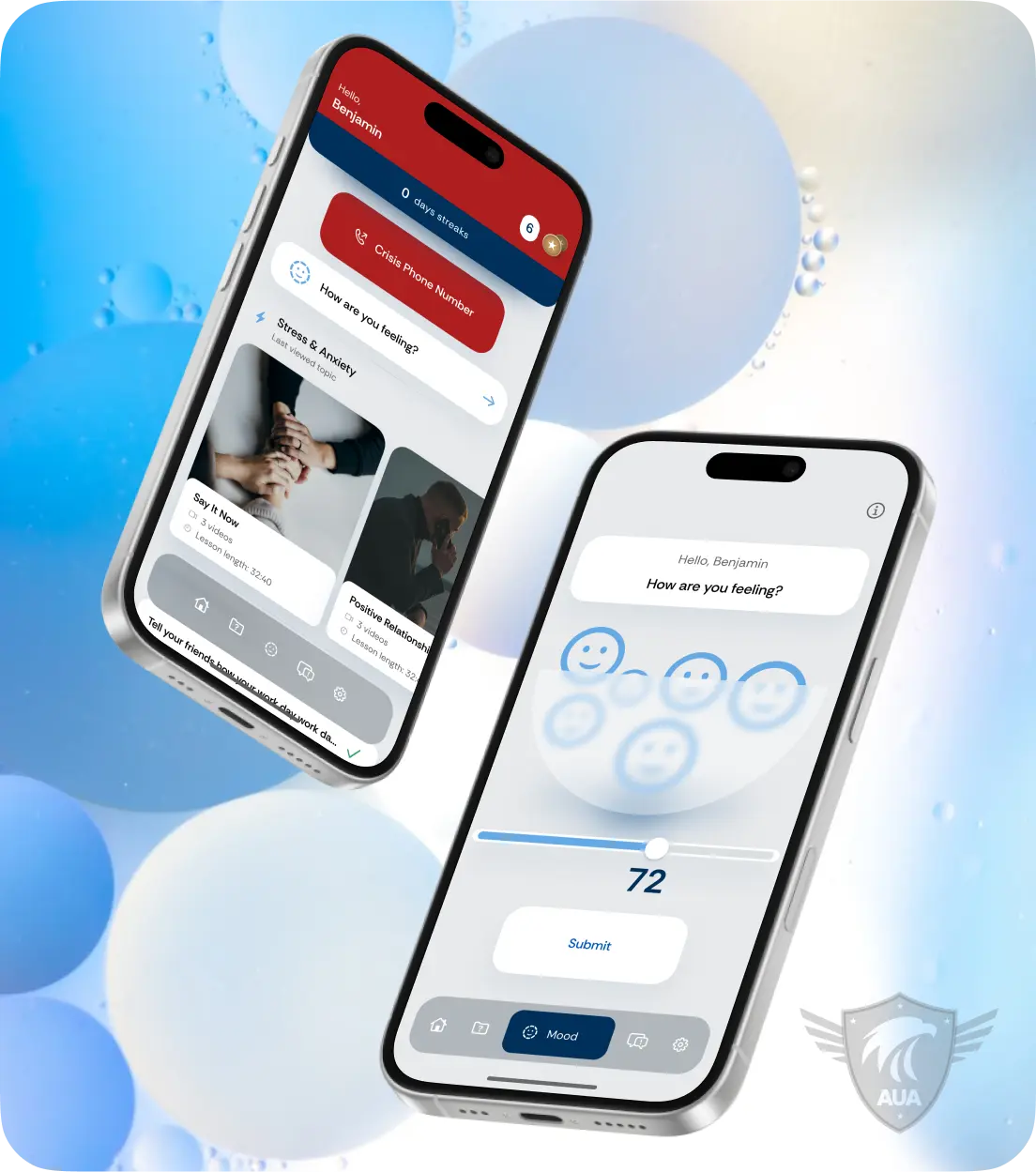
Armor Up America
Confidential mental wellness platform for U.S. first responders with peer support.

RAE Health
Healthcare platform with biomarker tracking and just-in-time support for patients.
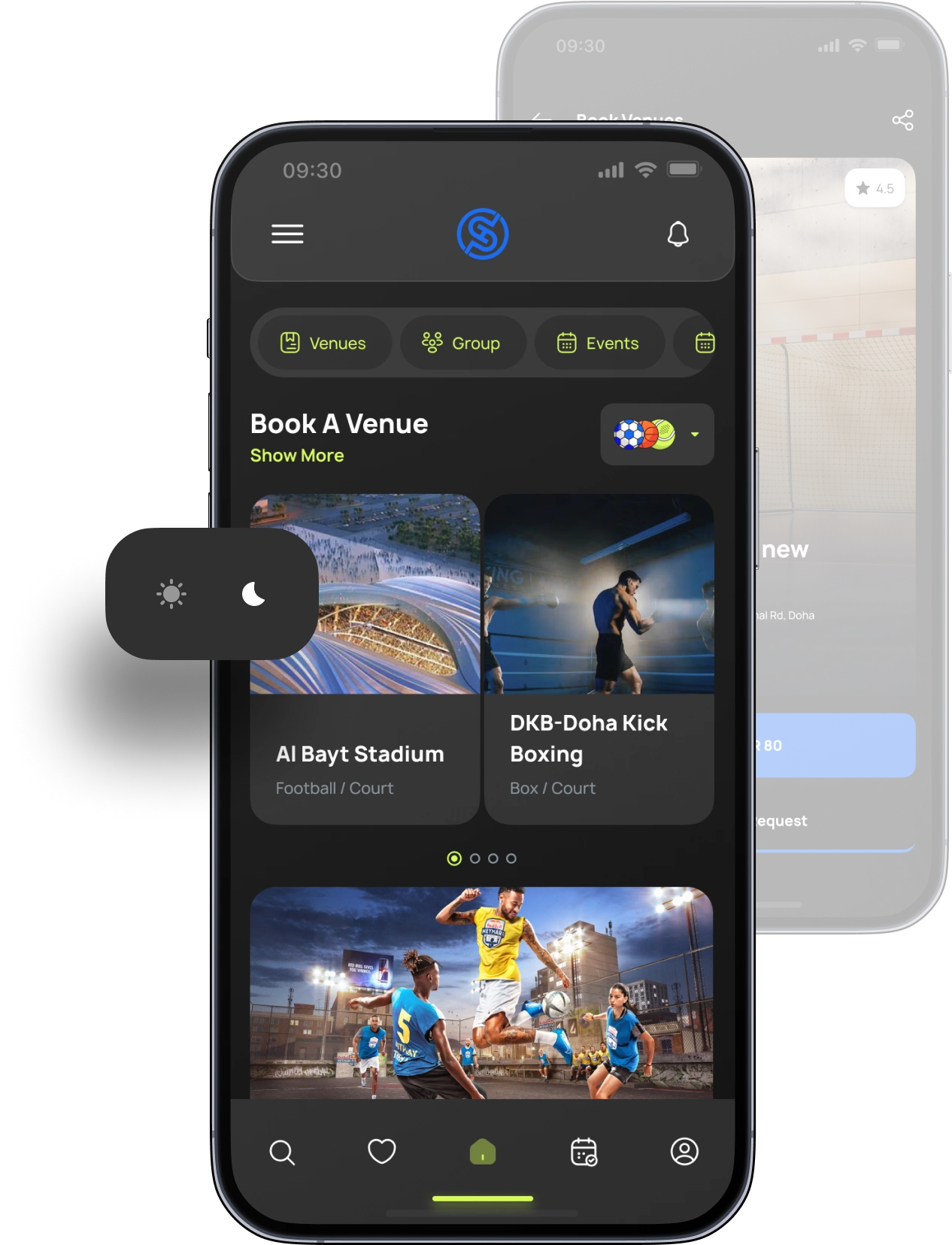
SportHub
Sports and lifestyle booking platform for venues, events, and memberships in Qatar.
Trusted in Healthcare Technology
See why healthcare organizations choose us for digital transformation
Ready to Transform Your Healthcare Services?
Get expert healthcare software development services to modernize your healthcare organization and improve patient outcomes.
